TL;DR:
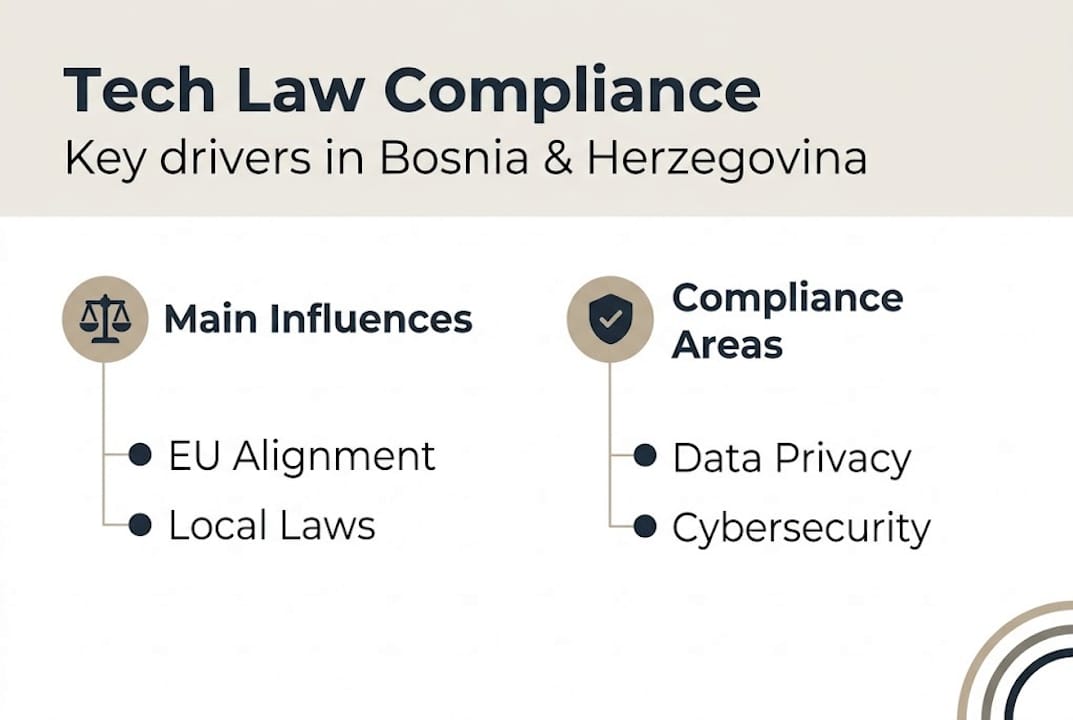
- Bosnia and Herzegovina's tech companies face evolving EU-aligned data protection and cybersecurity requirements.
- Proactive leadership and ongoing compliance practices are essential for regulatory adherence and risk management.
- Effective compliance involves detailed documentation, regular review, and strategic integration into business operations.
Technology companies operating in Bosnia and Herzegovina face a rapidly shifting compliance environment, where falling short of regulatory requirements can mean lost public sector contracts, significant financial penalties, and reputational damage that is difficult to reverse. Bosnia's alignment with EU data protection standards, combined with sector-specific cybersecurity demands and evolving procurement rules, has raised the bar considerably for technology firms of all sizes. This guide is designed to help business leaders and compliance officers understand the precise legal obligations they face, prepare the right documentation and internal structures, and implement a compliance programme that is both robust and sustainable.
Table of Contents
- Understanding the legal landscape for technology in Bosnia and Herzegovina
- Compliance prerequisites: What you need before starting
- Step-by-step technology law compliance process
- Ensuring compliance: Verification, adaptation, and common pitfalls
- Our perspective: Technology law compliance in Bosnia demands proactive leadership
- How we can help your business navigate technology law
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Know the rules | Understanding Bosnia’s evolving technology law is essential to avoid fines and business risks. |
| Prepare key documents | Have all compliance documentation ready, including records of processing and DPIAs. |
| Follow the steps | Use a systematic compliance process and watch for high-risk processing triggers. |
| Verify and adapt | Regular checks and quick adaptation to legal updates keep you compliant long-term. |
Understanding the legal landscape for technology in Bosnia and Herzegovina
With the stakes clear, it is vital to understand the specific legal terrain technology firms face. Bosnia and Herzegovina sits at a crossroads of EU harmonisation, regional trade obligations, and domestic legal reform, all of which directly affect how technology businesses must operate.
The country's technology law compliance framework is shaped by three principal drivers. First, the Stabilisation and Association Agreement (SAA) with the EU commits Bosnia to progressively aligning its laws with those of the European Union, including in the areas of data protection, electronic commerce, and cybersecurity. Second, membership of the Central European Free Trade Agreement (CEFTA) creates further cross-border obligations for technology businesses trading across the region. Third, Bosnia's domestic Law on Personal Data Protection, recently updated to align with the General Data Protection Regulation (GDPR), now sets binding standards for data processing, security, and accountability.
According to trade data on Bosnia's IT sector, the technology market in Bosnia and Herzegovina is characterised by low digitalisation overall, with significant and growing demand for cybersecurity solutions, data protection tools, and cloud services. The public sector remains the largest single customer, which carries a particular compliance implication: firms bidding for government contracts are increasingly expected to demonstrate data protection and cybersecurity credentials as part of the procurement process.
Understanding how compliance expectations have shifted is essential for any compliance officer. The table below illustrates the evolution from older to current requirements:
| Compliance area | Previous expectation | Current requirement |
|---|---|---|
| Data protection | Basic data handling | Full GDPR-aligned law, lawful bases, records |
| Cybersecurity | General IT security | Documented policies, risk assessments, reporting |
| Public sector contracts | Technical capability | Demonstrated compliance certification |
| Cross-border data transfer | Informal agreements | Structured transfer mechanisms, processor contracts |
| Breach notification | No formal obligation | Mandatory notification without undue delay |
Key regulatory requirements now facing technology firms include:
- Registration and maintenance of a record of processing activities
- Appointment of a Data Protection Officer where required by law
- Completion of Data Protection Impact Assessments (DPIAs) for high-risk processing
- Implementation of EU compliance frameworks for cross-border data transfers
- Formal processor contracts with all third-party data processors
- Documented cybersecurity incident response procedures
The website security checklist approach adopted in comparable professional services sectors illustrates just how granular these requirements now are. Technology businesses should expect similar scrutiny of their own digital infrastructure.
Compliance prerequisites: What you need before starting
Once the legal basics are clear, preparation is key. Here is how to set up for success before any formal compliance process begins.
Technology firms in Bosnia and Herzegovina must gather a specific set of documents and establish clearly defined internal roles before attempting to implement a compliance programme. Missing either the documentation or the accountability structure at the outset is one of the most common reasons compliance efforts fail or produce gaps that regulators later identify.

The following compliance mechanics are now legally mandated under Bosnia's updated data protection law: lawful basis for processing (which may include consent, contract, legal obligation, vital interests, public task, or legitimate interests), data protection by design and by default, records of processing activities, DPIAs for high-risk processing, DPO appointment where large-scale monitoring or sensitive data processing occurs, breach notification without undue delay, and formal processor contracts.
The essential documents to prepare before beginning include:
- Register of processing activities: A detailed record of every data processing operation, including the purpose, legal basis, data categories, and retention periods.
- DPIA template: A standardised template for conducting Data Protection Impact Assessments, ready to apply to any new high-risk processing activity.
- DPO appointment letter: Formal documentation of the Data Protection Officer's appointment, role, and responsibilities.
- Processor contract templates: Standard form agreements for engaging any third party that processes personal data on behalf of your firm.
- Breach notification procedure: A documented internal procedure covering detection, assessment, escalation, and notification to the relevant supervisory authority.
Alongside these documents, clearly defined roles are essential. The summary table below sets out which roles are required, who is typically responsible, and how frequently each obligation must be reviewed:
| Documentation or activity | Responsible role | Review frequency |
|---|---|---|
| Register of processing activities | DPO or compliance lead | Quarterly |
| DPIAs | DPO, with business owner | Per new high-risk activity |
| Processor contracts | Legal or compliance lead | Annually and at renewal |
| Breach notification procedure | DPO, IT security lead | Bi-annually |
| Staff data protection training | HR, DPO | Annually |
Data mapping is a prerequisite that many firms underestimate. Before you can complete a processing register, you need a clear picture of every system, application, or third-party tool that handles personal data. This includes internal HR systems, customer relationship management tools, cloud storage providers, and any SaaS products used operationally.
GDPR board-level responsibility is not merely a best practice; it is a legal reality. Leadership must be actively engaged in approving the compliance framework and allocating resources. Similarly, business confidentiality measures form part of the broader data governance structure, particularly for firms handling commercially sensitive client or partner information.
Pro Tip: Build a compliance calendar at the outset, with automated reminders for quarterly record reviews, annual training cycles, and contract renewal checks. Missed deadlines are avoidable with simple scheduling tools.
Step-by-step technology law compliance process
With your prerequisites ready, here is how to move from planning to execution.
A structured process is the most reliable way to achieve and sustain technology law compliance in Bosnia and Herzegovina. The following steps reflect the legal requirements currently in force and the practical realities of the country's regulatory environment.
Step 1: Map data processing and identify lawful bases
Begin by completing a full data mapping exercise across every department and system. For each processing activity identified, document the legal basis. A technology firm processing customer data for service delivery will typically rely on contract as the lawful basis. Marketing activities may require explicit consent. Compliance functions may invoke legitimate interests, provided a balancing test is properly recorded.
Step 2: Implement data protection by design and by default
This principle requires that privacy considerations are built into the architecture of any new product, system, or process from the very beginning, not added as an afterthought. Default settings must be configured to the most privacy-protective option. This is particularly relevant for software development firms building products for the Bosnian or regional market.
Step 3: Maintain robust records and perform regular DPIAs
Records of processing activities must be kept up to date, with any new or changed processing activity added promptly. High-risk processing, such as large-scale profiling, processing of biometric data, or systematic monitoring of individuals, requires a DPIA before the activity begins. A DPIA must identify the risks, assess their likelihood and severity, and document the measures taken to mitigate them.
Step 4: Appoint a DPO where required and manage processor contracts
Where a technology firm engages in large-scale processing of sensitive data or systematic monitoring, appointing a Data Protection Officer is a legal obligation. The DPO must be given sufficient resources and authority to operate independently. Every third-party processor must be bound by a contract that specifies the nature, purpose, and duration of processing, as well as the processor's obligations under law.
Step 5: Notify breaches and meet video surveillance legal standards
"Breach notification without undue delay is a legal requirement. Treat every suspected breach as a live compliance event from the moment it is detected."
Any personal data breach that poses a risk to individuals must be notified to the relevant supervisory authority. Where video surveillance systems are in use, a clear legal basis must be established, appropriate notices must be displayed, and access to footage must be strictly controlled. Review your startup legal checklist to confirm all foundational obligations are met before adding any monitoring technology.
Ensure your privacy policy requirements are fully reflected in all public-facing documentation. Technology firms frequently overlook the need to update privacy policies when new processing activities are introduced.
Pro Tip: Maintain a library of pre-approved DPIA and breach notification templates. When a high-risk activity is proposed or an incident occurs, having a ready template reduces response time significantly and ensures regulatory standards are consistently met.
Ensuring compliance: Verification, adaptation, and common pitfalls
You have launched your compliance programme. Now, focus on monitoring and evolving your efforts.
Compliance is not a one-time project. Technology law in Bosnia and Herzegovina continues to evolve, and firms that treat compliance as a completed task rather than an ongoing discipline are those most likely to face regulatory scrutiny.
Regular compliance checks should include:
- Quarterly review of the processing activities register to capture any new or changed activities
- Annual review of all processor contracts and DPO appointment documentation
- Monthly check of any updates to Bosnia's data protection law, EU-level GDPR guidance, or sector-specific cybersecurity regulations
- Bi-annual internal audit of breach detection and notification procedures
- Review of staff training records to confirm all relevant personnel have completed current training
The most common pitfalls that technology firms encounter are:
- Outdated records: Processing registers not updated when new systems or third-party tools are introduced.
- Missing DPIAs: High-risk processing activities launched without a completed impact assessment.
- Slow breach notification: Breach notifications delayed due to unclear internal escalation processes.
- Processor contract gaps: Engaging new third-party vendors without updating data processing agreements.
- Inadequate documentation: Relying on informal records that cannot withstand regulatory review.
The table below contrasts the characteristics of a fully compliant technology firm with those of an at-risk organisation:
| Characteristic | Fully compliant firm | At-risk organisation |
|---|---|---|
| Processing register | Current, reviewed quarterly | Incomplete or outdated |
| DPIAs | Completed before high-risk activities | Conducted retrospectively or not at all |
| Breach procedure | Documented and tested | Informal or undocumented |
| Processor contracts | In place and reviewed annually | Missing or generic |
| Staff training | Annual, with records | Ad hoc or unrecorded |
| Legal monitoring | Ongoing, assigned responsibility | Reactive only |
Understanding the scaling legal risks that accompany business growth is particularly important in this context. Firms that expand rapidly often outgrow their compliance structures before they realise it. Legal guidance becomes especially valuable at those inflection points. External document review support can also provide an independent check on the completeness and accuracy of your compliance documentation.
Pro Tip: Conduct a short monthly mini-audit focusing on one specific compliance area, such as processor contracts in January, DPIA records in February, and breach procedures in March. Rotating focus prevents blind spots from developing and keeps compliance active rather than passive.
Our perspective: Technology law compliance in Bosnia demands proactive leadership
Many technology firms in Bosnia and Herzegovina approach compliance as a box-ticking exercise, completing the minimum documentation required and moving on. This carries real risk. The regulatory landscape is not static. EU legal developments feed into Bosnia's domestic law through the SAA harmonisation process, meaning that what was compliant last year may be insufficient today.
The firms that handle this environment most effectively treat compliance as a strategic function, not an administrative burden. Board-level ownership of data protection and cybersecurity obligations changes the culture of compliance throughout the organisation. When leadership actively monitors the regulatory environment and allocates genuine resources to compliance, the entire business becomes more resilient.
The real-world compliance insights that matter most are not found in the formal text of the law. They come from understanding how regulators interpret the law in practice, how procurement officers assess compliance credentials, and how quickly a firm can respond when something goes wrong. Proactive adaptation to legal change, rather than reactive correction after the fact, is what distinguishes compliant technology businesses from vulnerable ones.
How we can help your business navigate technology law
If you are ready for next-level compliance, specialist support can make all the difference.
Vucic.legal brings deep experience advising technology businesses on regulatory compliance in Bosnia and Herzegovina and across the wider European market. Our strategic legal services cover every dimension of technology law compliance, from initial compliance audits and documentation reviews to ongoing Data Protection Officer support and legal monitoring as the regulatory environment evolves.
Whether your firm is at the early stages of building a compliance framework or seeking to strengthen an existing programme, our team can provide structured, practical support tailored to your operational context. Download our compliance checklist for Bosnia to assess your current position, or contact us directly to discuss how legal guidance can support your next phase of growth.
Frequently asked questions
Who must appoint a Data Protection Officer in Bosnia and Herzegovina?
Any technology company engaged in large-scale monitoring or sensitive data processing is legally required to appoint a Data Protection Officer under Bosnia's updated data protection law. The DPO must have sufficient expertise and operate with genuine independence within the organisation.
What records must tech firms keep for compliance?
Firms must maintain records of processing activities, completed DPIAs for high-risk processing, evidence of lawful bases for each processing activity, and documentation of all processor contracts. These records must be kept current and available for regulatory review on request.
Are there special rules for biometric and surveillance data?
Yes. High-risk processing such as biometrics or video surveillance requires both a completed DPIA and a clearly established legal basis before processing begins. Video surveillance additionally requires visible notice to individuals and strictly controlled access to recorded footage.
What is the main compliance challenge in Bosnia's tech sector?
Rapid legal harmonisation with EU standards, combined with low digitalisation and cybersecurity demand, means technology firms must continuously update their compliance frameworks while simultaneously strengthening their technical security infrastructure. Static compliance programmes quickly become inadequate in this environment.
